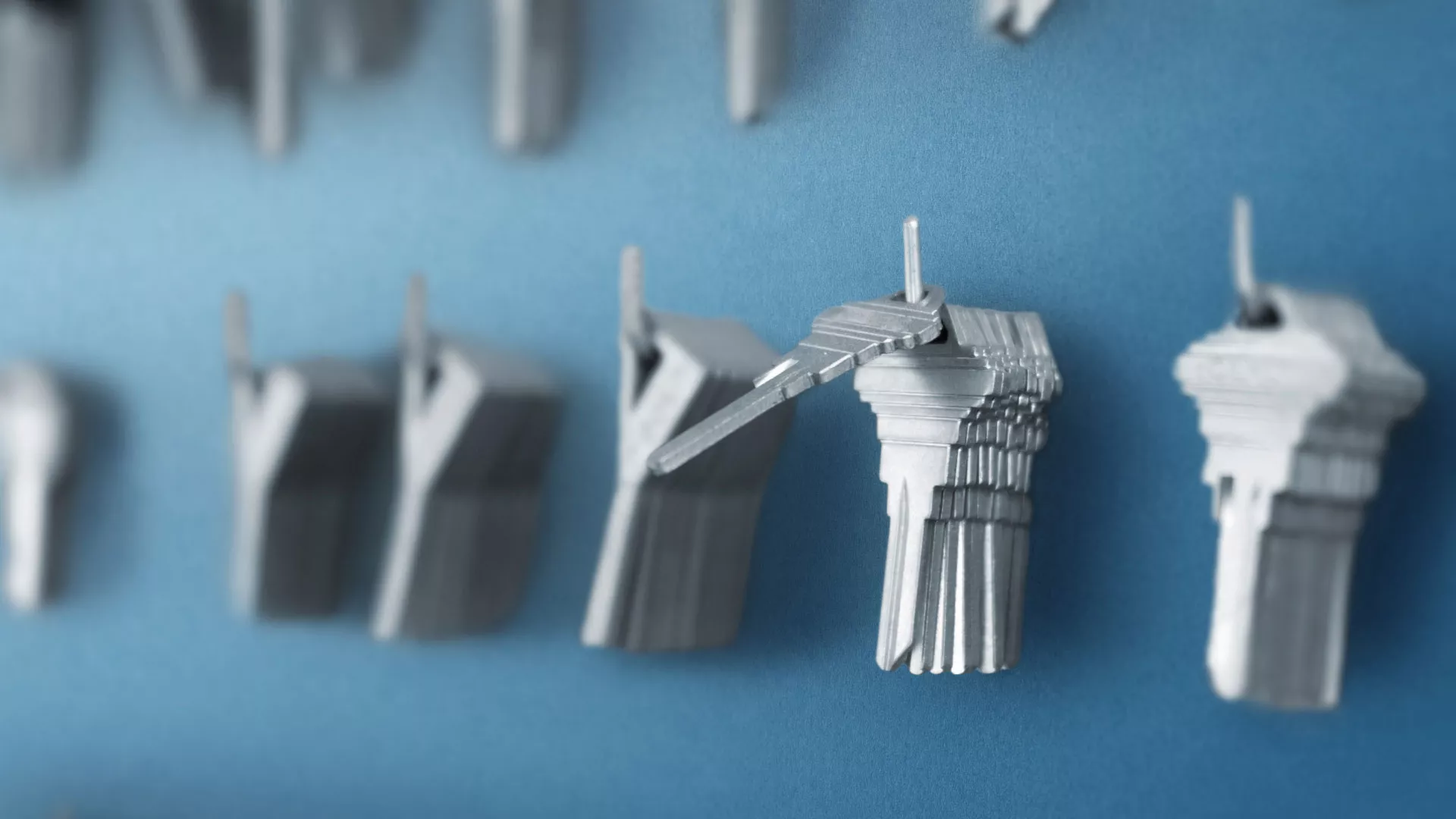
Every organization faces the challenge of managing its cryptographic keys.
Simplifying Cryptographic Key Management
As data volumes increase and security threats multiply, the task of safeguarding sensitive information becomes increasingly challenging. The key to effective data protection lies in the management of cryptographic keys - yet, this process often demands significant time and effort. Centralizing cryptographic key management emerges as the foremost challenge for organizations seeking to enhance their security posture. Beyond centralized and streamlined management of their consolidated key inventory, organizations seek a solution that upholds the highest standards of security, compliance, and tamper-resistance. Additionally, role-based access is essential to ensure that only authorized personnel can access and manage critical encryption keys, thereby fortifying data security at every level.
Key Management made easy by UTIMACO
Utimaco simplifies the complexities of key management, offering secure on-premises and as a Service Key Management solutions to address the challenge of managing crypto secrets.
Our comprehensive key management offerings encompass the entire lifecycle of cryptographic keys - from generating and storage to provisioning, access control, and auditing. Whether you choose on-premises deployment or cloud-based services, UTIMACO ensures that your organization's critical encryption keys are protected and managed securely -
preserving access to business-critical, sensitive encryption keys.
By separating encryption keys from the data they protect, our Key Management solutions provide a vital layer of security, preventing access to both keys and encrypted data. Even if your database is compromised, your data remains secure, preserving the integrity and confidentiality of your most sensitive information.
Streamline your key management processes, reduce your costs, and minimize the risk of human errors with Utimaco’s Key Management solutions.